Recently I received an email entitled “Domain Abuse Notice: DomainName”, as its been over 10 years I am into this industry, I was pretty sure about something wrong. Then I checked with other emails and to my surprise, I received same email from different persons. Here is the text from those emails:
Dear Domain Owner,
Our system has detected that your domain: DomainName is being used for spamming and spreading malware recently.
You can download the detailed abuse report of your domain along with date/time of incidents. Click Here <Link>
We have also provided detailed instruction on how to delist your domain from our blacklisting.
Please download the report immediately and take proper action within 24 hours otherwise your domain will be suspended permanently.
There is also possibility of legal action depend on severity and persistence of your abuse case.
Three Simple Steps:
- Download your abuse report.
- Check your domain abuse incidents along with date and time.
- Take few simple steps for prevention and to avoid domain suspension.
Click Here to Download your Report <Link>
Please look into it and contact us.
Best Regards,
Domain Abuse Admin
DomainCop Inc.
Tel.: (139) 723-31-04
The email body was exactly same in all emails I received and here is the list of different senders who sent those emails:
- Alfie Robinson ([email protected])
- Theo Moore ([email protected])
- Muhammad Lewis ([email protected])
- Olivia Parker ([email protected])
- Toby Mitchell ([email protected])
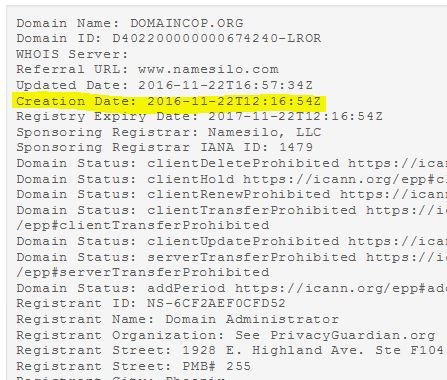
I did a quick research and found that the DomainCop.org was registered on 22nd Nov 2016 (1 day before) and here is the whois information:
Now, a one day old domain (so called business) started analyzing domain and circulated mass emails. The motive seems very clear to threaten webmaster to visit those links. I did quick search on Google to learn about other webmaster’s response and found this detailed blog post about explaining this spam.
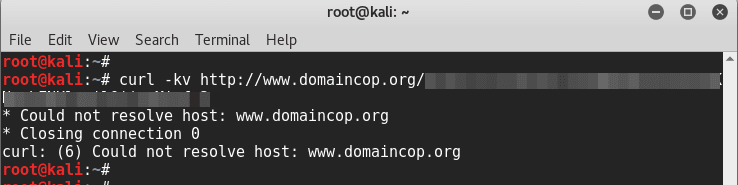
The author did a detailed analysis about this domain abuse notice email from DomainCop and found that the domain has no DNS response when tested on cURL and with dig command. Received NXDOMAIN response which means the domain doesn’t exists in DNS.
If you ever receive any of such email, here is the steps you should always follow before clicking on any links or resources:
- Check Domain Whois
- Check the URL without actually going into it.
- Use online scanners to check the link
- Check DIG/NSLookup info
- Search in Google
- If you must visit the URL, do it from a command line tool or from a VM.
Don’t worry and follow given steps to avoid any issue when you receive such emails. Here I recommend visiting specified blog post has beautifully explained the entire scenario and recommended lot of resources and tools for spam check the domain or email.